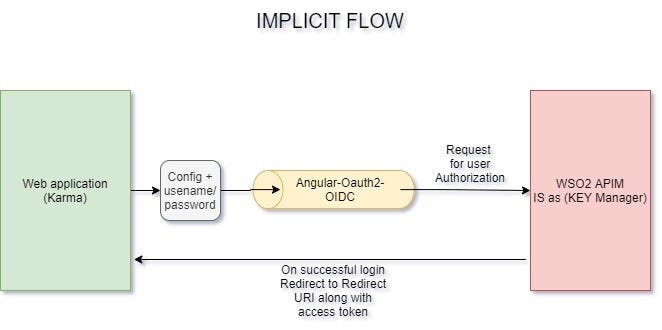
Angular oauth2 oidc implicit flow example
Already prepared for the upcoming OAuth 2. Successfully tested with Angular 4. At server side we've used IdentityServer. For Auth0, please have a look into the respective documentation page here.
Browser vendors are implementing increasingly strict rules around cookies. Most notably problems occur if the "silent refresh via an iframe" technique is used. This repository uses that technique currently, starting with a silentRefresh. This will fire up an iframe to load an IDS page with noprompt , hoping cookies get sent along to so the IDS can see if a user is logged in. In fact, if you fire up this sample repository on localhost , which talks to demo. For reference, see issue 40 , or my blogpost that explains workarounds and solutions.
Angular oauth2 oidc implicit flow example
When package installation has been done then import the OAuthModule in the app. It sends the user to the IdentityProvider's login page Identity Server. After logging in, the SPA gets tokens. This alsoallows for single sign on as well as single sign off. To configure the library just have to set some properties AuthConfig on startup as requiredby OAuthService i. The discovery endpoint can be used to retrieve metadata about your IdentityServer - it returns information like the issuer name, key material, supported scopes etc. You can adjust this factor by setting the property timeoutFactor to a value between 0 and 1. For instance, 0. In order to log out from the application, just need to call the logout method of theOAuthService. Thank you. I am having issues authentication my app against my api.
Ensure you have your issuer set to your discovery document endpoint!
Map with additional query parameter that are appended to the request when initializing implicit flow. Names of known parameters sent out in the TokenResponse. Of course, when disabling these checks then we are bypassing a security check which means we are more vulnerable. You can disbale it here by setting this flag to true. In this case, you can set a password here.
Already prepared for the upcoming OAuth 2. Successfully tested with Angular 4. At server side we've used IdentityServer. For Auth0, please have a look into the respective documentation page here. For using this library with Azure Active Directory Azure AD , we recommend an additional look to this blog post and the example linked at the end of this blog post. Also, the Okta community created some guidelines on how to use this lib with Okta. See the links at the end of this page for more information. Angular 17 : Use
Angular oauth2 oidc implicit flow example
The OpenID Connect code flow with PKCE uses refresh tokens to refresh the session and at the end of the session, the user can logout and revoke the tokens. The demo is setup to use each refresh token only once. Sometimes it is required to load the configuration from an HTTP address. You can load the configuration from your source and map it into the required format using the loader property on the. The example logins the user in directly without a login click using the code flow with PKCE and an auth-guard. Identity provider is implemented using node-oidc-provider. The is a multiple configurations sample which uses Auth0 with refresh tokens for one configuration and IdentityServer4 for the second. The is the multiple configurations sample which uses Auth0 with refresh tokens for one configuration and IdentityServer4 for the second. Popups are used to authentication. The example uses the Open ID Connect implicit flow with iframe renew.
Itunes ipad
Sep 20, Defines whether to use OpenId Connect during implicit flow. Angular 12 : Use As this password is exposed to the public it does not bring additional security and is therefore as good as using no password. Angular 10 : Use Defines whether to request an access token during implicit flow. Since that was considered a bug , the need to do so was removed. Feel free to open an issue and PR if you want to add additional pieces of guidance to this section. Map with additional query parameter that are appended to the request when initializing implicit flow. Option 2: Using NgModules. There are various other server side solutions available, each with their own intricacies. This alsoallows for single sign on as well as single sign off.
Browser vendors are implementing increasingly strict rules around cookies. Most notably problems occur if the "silent refresh via an iframe" technique is used. This repository uses that technique currently, starting with a silentRefresh.
See the documentation for more information about this library. Set this to true if you want to use silent refresh together with code flow. Defines whether additional debug information should be shown at the console. You can also try the newer version 5. Of course, when disabling these checks then we are bypassing a security check which means we are more vulnerable. Log in Create account. Public Optional checkOrigin. Latest commit History Commits. The auth server's endpoint that allows to log the user in when using implicit flow. Use lower case for the prefixes. Defined whether to skip the validation of the issuer in the discovery document. Public Optional disableAtHashCheck.

The matchless phrase, is pleasant to me :)
It is exact
What entertaining answer